The vulnerability affects PHPMailer in versions prior to 5.2.18, and was discovered by Polish researcher Dawid Golunski.
At the time of writing, Golunski has not disclosed the technical details of the vulnerability, but he did say that the weakness can be exploited through website components such as registration forms, contact or feedback forms, and password reset features that use an affected version of PHPMailer for sending Е-Mails.
Upon a quick difference check, we can see that the vulnerable code lies in the following lines of the class.phpmailer.php:
Version < 5.2.18
if (!empty($this->Sender)) {
$params = sprintf('-f%s', $this->Sender);
}
if ($this->Sender != '' and !ini_get('safe_mode')) {
$old_from = ini_get('sendmail_from');
ini_set('sendmail_from', $this->Sender);
}
Version >= 5.2.18
if (!empty($this->Sender) and $this->validateAddress($this->Sender)) {
$params = sprintf('-f%s', escapeshellarg($this->Sender));
}
if (!empty($this->Sender) and !ini_get('safe_mode') and $this->validateAddress($this->Sender)) {
$old_from = ini_get('sendmail_from');
ini_set('sendmail_from', $this->Sender);
}
In the vulnerable version of PHPMailer, the sender Е-Mail address is passed "unescaped" to a shell command. An attacker could then include shell commands in the sender Е-Mail that execute malicious code on a target machine or website.
To fix the issue, we recommend that you update the PHPMailer library to version 5.2.18 or later, by replacing the file commonly named 'class.phpmailer.php' within your website's files.
If you're running an open source application such as WordPress, Drupal, Magento or other such applications, we'd recommend ensuring that it is updated along with any plugins/extensions.
How are we protecting our customers?
If you are a Kualo shared or reseller hosting customer, then our Patchman system will have automatically detected vulnerable versions of PHPMailer within the applications that it is capable of scanning, such as WordPress. These files will be automatically patched within a few hours. If you'd like to manually trigger a patch before they are automatically updated, simply login to your cPanel and go to: Advanced Patchman Actions Patch: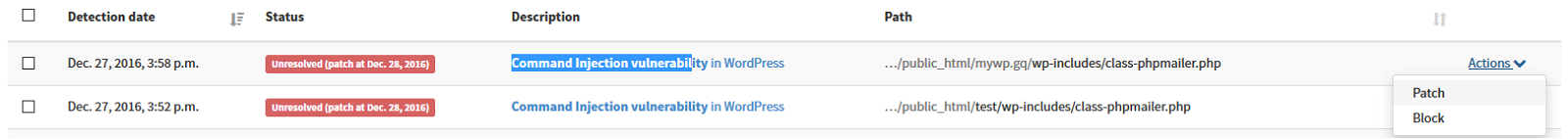
Should you need any further assistance, please do not hesitate to contact us.